Artificial intelligence; its business usage, current landscape, road ahead

By Jessica Xieyang Qiao Medill Reports Artificial intelligence is coming into the mainstream. Still, a host of challenges remain. On this episode of Medill Newsmakers, we talk to Chicago-based machine learning engineers and chief technology officers to explore key challenges and opportunities facing AI. Photo at top: Machine learning-based techniques can be used to solve […]
A mosquito can become a video game hero in Japan

By Jessica Xieyang Qiao Medill Reports A lone mosquito patrols the Yamada family to stock up on blood for the coming winter. You are Mister Mosquito, an uninvited guest who pesters the hapless Yamada family. They want you dead. You want to bite. The battle is on. Quirky as it sounds, Mister Mosquito is a […]
New cyberattacks such as cryptojacking make past risks kids’ stuff
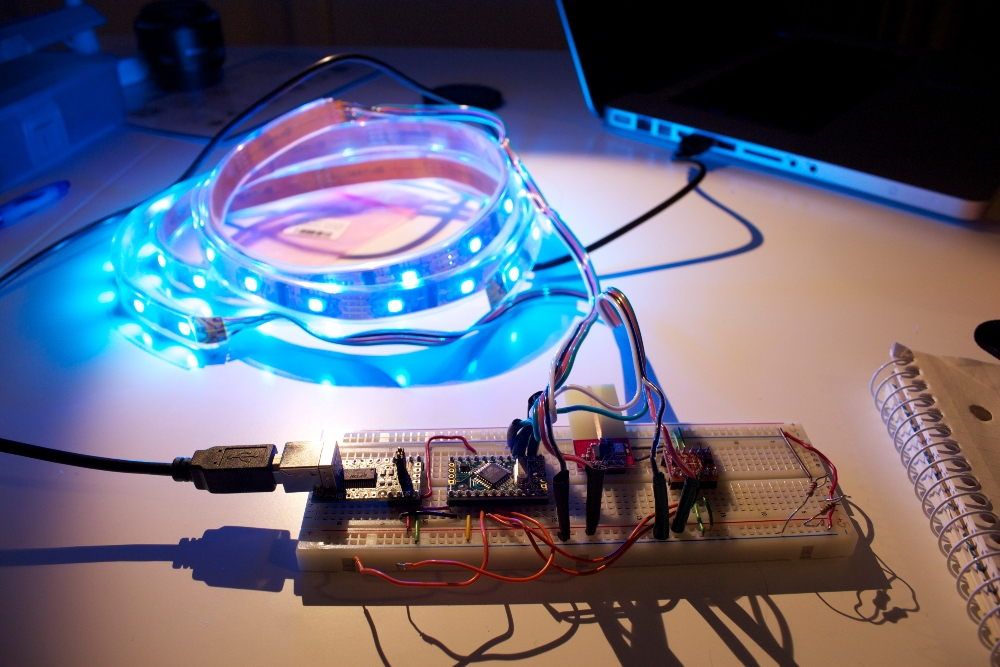
By Xieyang Jessica Qiao Medill Reports Blockchain, AI, IoT and a storm of new technologies are leading to greater operational efficiency and consumer opportunities, while triggering an increasing range of cyberattacks. In the age of digital transformation, the best defense for users is to understand past breaches in order to maintain constant vigilance for future […]
Most trendy 2018 technologies unveiled in Chicago and beyond

By Xieyang Jessica Qiao Medill Reports Today may be the slowest day you’re ever going to have during the rest of your life. The pace of change tomorrow will be faster than the pace today. Chicago’s burgeoning VC opportunities and tech scene An entrepreneurial spirit, fueled by investors who bet big on the city, is […]
Cyber insurance: Consumer friend or foe?

By Jessica Xieyang Qiao Medill Reports Warren Buffett is not eager for Berkshire Hathaway to be a pioneer in the “uncharted territory” of investing in cyber insurance. Yet cyber insurance is growing and evolving rapidly in response to a surge in demand and an increasing level of cyber threats. The total cybersecurity insurance market in […]
Chicago hardened controls on cybersecurity with heightened concerns about electronic voting

By Jessica Xieyang Qiao Medill Reports Amid the ongoing 2019 mayoral elections and an increasing number of nationwide data breaches, Chicago beefed up cybersecurity controls to defend against potential voter fraud and hacking. Yet, the cybersecurity environment remains flawed and technology challenges facing the government cast doubts on maintaining the reliability of electronic voting, according […]
Japanese and Illinois companies connect for Industry 4.0

By Jessica Xieyang Qiao Medill Reports Japan, a hotbed of craftsmanship and innovation, is well equipped for the fourth industrial revolution as Japanese manufacturing companies leverage high technology to accelerate the delivery of industrial automation solutions. Panasonic System Solutions Company of North America (PSSNA), a subsidiary of Panasonic Corporation, launched in April last year to […]
Demystifying artificial intelligence, machine learning and deep learning

By Xieyang Jessica Qiao Medill Reports Artificial intelligence (AI), machine learning (ML), and deep learning (DL) – these buzzwords are used so interchangeably that they become fluid in interpretation. But while these emerging technologies are intertwined, they provide different levels of application. DL is a subset of ML, and ML is a subset of AI, […]
Break down silos to make Chicago an electric transit leader

By Xieyang Jessica Qiao Medill Reports As vehicle automation and electrification gain traction, they create a new mobility ecosystem for Chicago to tap into. Yet the city’s traditional residential infrastructure and limited connectivity could hinder Chicago and other metropolises in their ability to innovate. Waymo, Google’s autonomous car subsidiary, announced last year they would purchase […]
5G rollout brings to life the smart hospital

By Xieyang Jessica Qiao Medill Reports Chicago-based Rush University Medical Center partnered with AT&T to deploy a fifth-generation cellular network in hospital settings, capitalizing on 5G’s fast speeds to enhance access to care and improve efficiency. 5G is expected to operate in the millimeter wave band, which has a much higher frequency than current bands […]

