By Xieyang Jessica Qiao
Medill Reports
Blockchain, AI, IoT and a storm of new technologies are leading to greater operational efficiency and consumer opportunities, while triggering an increasing range of cyberattacks.
In the age of digital transformation, the best defense for users is to understand past breaches in order to maintain constant vigilance for future threats.
AI applications have made inroads in robotic process automation that allows users in all professions to extract key metadata from their text, including entities, relations, concepts and sentiments. This helps lawyers run a smarter practice, for instance.
“Process automation can extract basic entities from your contracts’ metadata across different repositories and move that metadata into a contract life cycle management system,” said Andrew Pery, consultant of ABBYY, a software company that offers AI-based solutions. “So you have a single point of resources from which you can manage the contract life cycle.”
More advanced instances of process automation focus on cognitive analytics. By using the neural network, natural language processing and semantic analysis, AI extracts meaning from legal documents and may even predict the outcome of a court case.
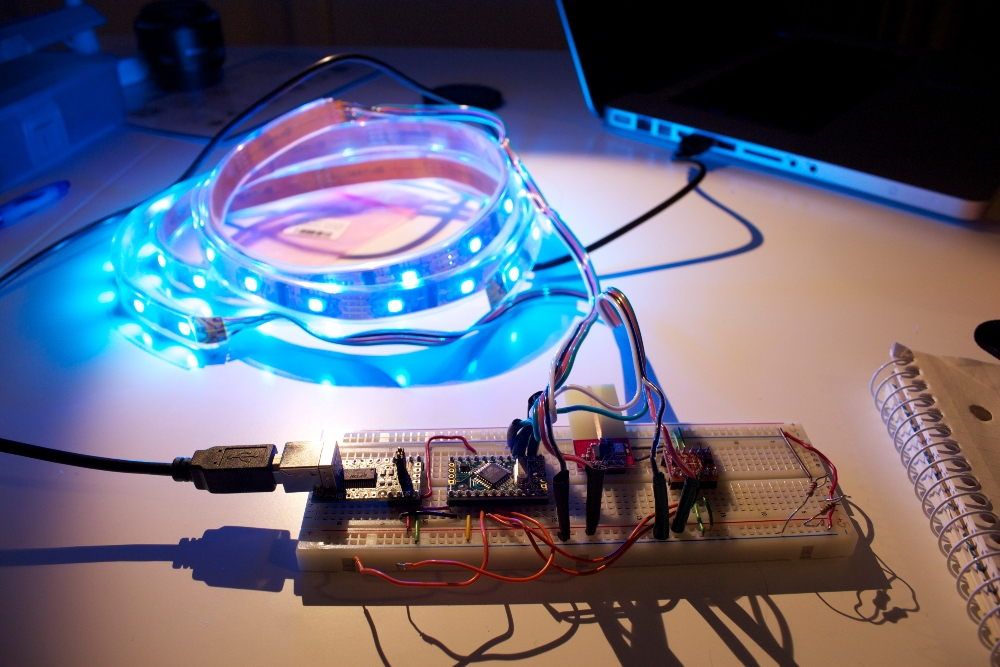
While high technology generates excited chatter with its wide-ranging applications, it also creates new security incidents that have become increasingly complex. Recent years saw the growth of malware attacks targeting AI-powered and IoT devices.
“Everything that is connected to the internet is potentially susceptible to data breaches, and getting attached to the internet can become in essence a risk factor,” said Tomas Suros, chief solutions architect of AbacusNext, a software and private cloud services provider. “We’ve seen attacks specific to those AI-powered or IoT devices. Malware may propagate through Alexa, Siri or anything that can be used to automate activities.”
Suros said 60 percent of small- and medium-sized businesses had been infected or had a data breach at one point. Within six months, 60 percent of them went out of business.
“The scope of malware attacks is increasing,” Suros said. “The damage to your business reputation, your inability to restore and the cost associated with recovery are devastating.”
While the sophistication of cyber crimes increases, its paradigm also shifts. A hacker breaks into your network to steal information or creates a virus to corrupt your network are now “ancient” models of cyberattacks. The new culprit is no longer smash-and-dash.
“Let’s say somebody inadvertently clicks on a link in an email,” Suros said. “The malware attack may not happen immediately. Instead, a bot is dropped on your network. It does password sniffing and siphons off that information in a way that is not immediately apparent. But the bot can penetrate your network and continue to do damage.”
There is also a nefarious nature to the way these innovative attacks are initiated, as they spike immediately before and after Thanksgiving and Christmas breaks.
“The goal is to find you in a weak moment when you’re busy or distracted and all it takes is one weak point in your network to initiate a deadly infection,” Suros said.
One type of malware is Trojan, which purports to be a legitimate software such as a browser or an add-on. When you install the software, however, Trojan drops malware on your system.
“After the infection starts, Trojan can identify an encrypted network drive even a couple of layers deep,” Suros said. “If you have data drives that create backups, Trojan can come in to create an infection and find those drives. Before initiating the attack, it actually has a map. This allows Trojan to hide its traps and potentially remove your ability to restore your backups of that data.”
Ransomware, a subset of malware programmed to encrypt data and block access to the computer network until money is paid, ramped up last year and is likely to rise even more in 2019.
“It comes in many shapes and sizes,” Suros said. “One of the newer variants is described as artisanal, meaning it’s designed to know its targets, what systems they’re using, and then deploy itself in ways that fool individuals by giving them information that seems familiar.”
Samsam, the ransomware used in targeted attacks, is responsible for the 2018 Atlanta cyberattack when one-third of the 424 software programs used by the city were thrown offline or partially disabled.
“Samsam doesn’t immediately start an attack,” Suros said. “It starts a scheme by recognizing the system and looking for vulnerabilities – the shortest path to a disruptive attack. It may install a crypto miner or a keystroke logger, which keeps records of every keystroke and sends them off as a file. People can deconstruct that and find your password.”
Then there’s cryptojacking – an emerging form of ransomware that may hide on your network to gain unauthorized use of your computer to mine cryptocurrency.
“It’s not encrypting your data or preventing you from using the system,” Suros said. “But it uses your resources, your central processing unit (CPU) cycles, your storage and your internet to create cryptocurrencies and send that to someone else who collects them.”
While cryptojacking malware doesn’t take all your data, it steals your resources, slows down your system and limits your security shields.
Last year also saw an upward trend in spear phishing and whaling attacks. While whaling attack is a more specific type of spear phishing that targets high-level executives, both are social engineering attacks that use psychological manipulation to trick users into revealing sensitive information.
“Spear phishing can identify your organization,” Suros said. “It may appear to come from HR, requesting you to update your password. You may receive an email from the IT department, asking you to do something and you will probably do it- thinking that the cause is to improve your technology and security.”
Suros said attacks cost businesses more than $75 billion per year- and it’s not just ransom that is paid. If individuals refuse to pay ransoms, they no longer have access to their servers or workstations.
“They are out of business until they can restore and recover,” Suros said. “There are 1.5 million phishing sites being created each month. This has become an industry and it will continue to grow this year.”